Next Generation Enterprise Security Risk Management
 March/April 2022 | COVER STORY
March/April 2022 | COVER STORY
The Fourth Industrial Revolution is here. We live and work in an interconnected world in which machines, devices, sensors, and people connect and communicate with each other. We are surrounded by smartphones, Internet of Things (IoT) devices, location detection technologies, advanced human–machine interfaces, cyber–physical systems, cloud computing, authentication tools, fraud detection measures, smart sensors, advanced analytics capabilities, and digital customer profiling. Smart cities are coming online, with operators able to access enormous sets of information to manage systems.
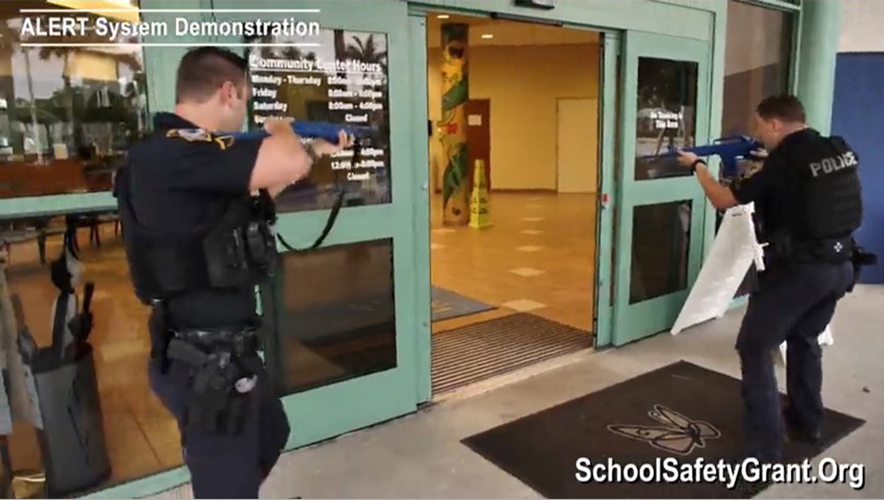
These technologies are transforming the global industrial landscape, and they are changing enterprise security risk management (ESRM) in ways the security industry is only starting to understand.