2022 ISC West Product Showcase
Print Issue: March/April 2022
Check out the latest security technologies, services, and solutions in this special edition product showcase.
For a limited time, download the March/April 2022 edition of Security Management, including the ISC West Product Showcase, here.
Touchless Intercom Systems
Hanwha Techwin’s TID-600R Network Intercom Station offers a touchless call system where users can simply present their palm within six inches of the station to initiate a call. The unit features a 2MP sensor with Hanwha Techwin’s signature WDR and IR. The station also features echo cancellation, noise reduction, and a built-in tamper switch and relay for standalone door access. Users can create audio messages to be played when the device is approached or upon call initiation. It can also integrate with various VMS, access control, SIP phones, or PBX servers. Visit hanwhasecurity.com/product/tid-600r to learn more. Stand 14079.
 Access Control
Access Control
AirAccess from NAPCO is a cell- and cloud-based hosted access system, powered by StarLink cellular communications. No server or on-site security staff is needed; instead, the system is scalable and easy to add on to doors with wireless smart locks that retrofit any standard locks or use standard identification readers with wireless panels. AirAccess also offers an app with built-in mobile credentials, text alerts, and lockdown—all for a flat monthly rate per system. Visit airaccesscontrol.com to learn more. Stand 12031.
Tailgate Prevention
Detex offers panic hardware for restricted secure areas and internal departments, including building entrances, manufacturing facilities, office entrances, fitness centers, corporate offices, and record rooms. The hardware aims to deny unauthorized entry while smoothly facilitating authorized entry. The Tailgate Detection System offers operations a chance to limit access to one identified entrant without giving tailgaters a free pass. The solution is compatible with most access control technologies, can be retrofitted, and features an integrated door prop alarm for additional security. Visit detex.com to learn more. Stand 13114.
Key Management
Morse Watchmans, Inc., offers signature key management systems that have customizable modules to secure all facility keys and assets, including wallets, cell phones, laptops, and small weapons. The company is dedicated to helping businesses maintain a secure and safe environment, and it looks forward to developing more progressive business security products in the future. Visit morsewatchmans.com to learn more. Stand 15109.
 Logistics Software
Logistics Software
Technology from TEAM Software by WorkWave offers security contractors increased efficiency and a chance to streamline operations. This holistic software gives users a way to keep an eye on all the moving parts of a business—insight into employee engagement, customer satisfaction, and overall efficiency allows for data driven decisions. Visit www.teamsoftware.com/industries/security-guard-software to learn more.

Cabinet Locks
ASSA ABLOY’s new HES KS210 integrated access control server cabinet lock offers enhanced security communications, monitoring, and credential options with integrated RS-485 OSDP and BLE technology. These locks provide a way to protect mission-critical data and equipment across an organization. Visit hesinnovations.com to learn more. Stand 8061.
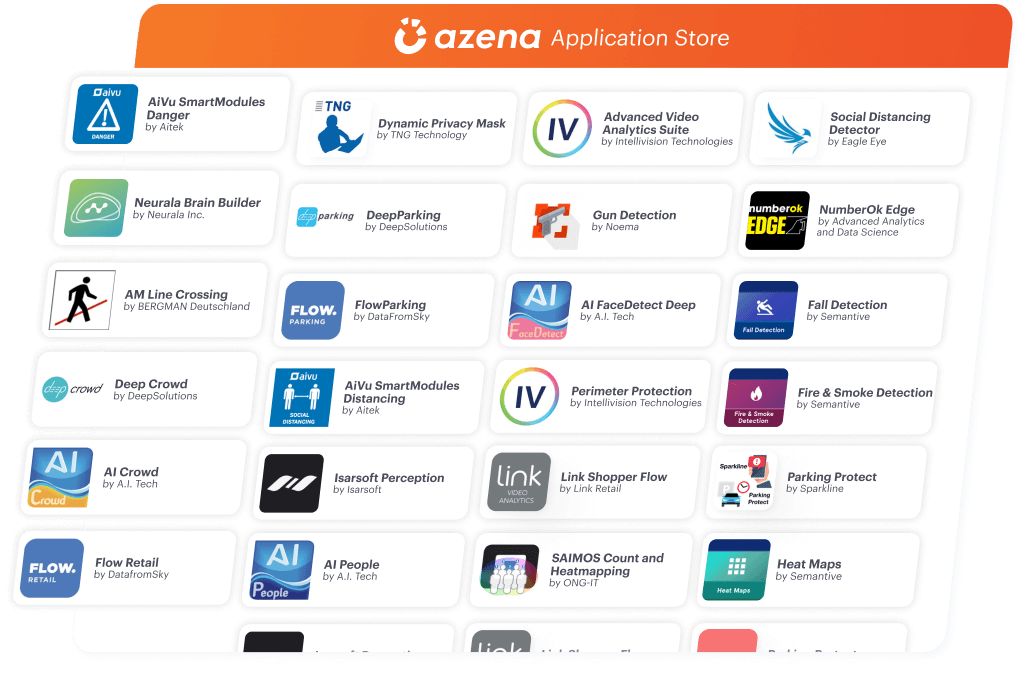 Video Analytics
Video Analytics
Azena’s platform for smart cameras offers ready-to-use artificial intelligence-enhanced video analytic applications, which can run directly on a smart camera to provide flexible video analytics solutions for unique business needs. More than 100 apps are available in the Azena applications store for smart cameras, offering solutions for retail, manufacturing, logistics, parking, stadiums, and more. The Azena camera operating system allows cameras to simultaneously run several apps downloaded to the cameras and changed based on customer needs. Visit azena.com to learn more. Stand 23075.
 Mail Screening
Mail Screening
RaySecur’s MailSecur solution offers the first U.S. Department of Homeland Security Safety Act-designated millimeter wave (mmWave) desktop scanner that can see into mail and packages to detect threats, including liquids, powder, explosives, weapons, radioactive materials, and other suspicious contents. The solution features a resolution 10 times greater than airport scanners and 300 times more sensitive than x-rays when it comes to detecting liquids and powder. MailSecur includes the turnkey EODSecur mail security program, which includes training, development of standard operating procedures and response plans, and one-touch, around-the-clock access to trained military Explosive Ordnance Disposal professionals who can immediately assist users working to resolve a threat. Visit raysecur.com/mailsecur to learn more. Stand 21125.
 Threat Detection
Threat Detection
Ontic’s real-time threat detection offering connects the entire threat management landscape and investigation process for Fortune 500 and emerging organizations, offering a picture of the risks that an entity faces. Key features include high-impact weather alerts and categorization connected to workflows that can activate a coordinated response; interactive and layered visualization of critical signals from OSINT, social media, the Dark Web, and news sources; continuous gathering of real-time and historical data; and customizable alert configurations for active events and known risks to assess threat relevance related to important people and places. Visit www.ontic.co to learn more. Stand 5059.
 External Power Supply
External Power Supply
Beginning in Q2 2022, ComNet will introduce two hardened PoE power injectors for applications where higher requirements for PoE power. The CNGE1IPSBT hardened Ethernet PoE power injectors meet the IEEE802.3bt standard and can supply power to devices requiring more power than provided by IEEE 802.3 at/af. The unit is AC-powered and the CNGE1IPSBT/DC model is DC-powered. Both models feature auto-detection of powered devices and are ideally suited to fiberoptic, wireless, or other networks where there may be difficulty in furnishing operating power to the powered devices. Visit www.comnet.net to learn more. Stand 30070.
 Guardhouses
Guardhouses
Par-Kut offers an enhanced bullet-resistant security booth, developed in collaboration with the integrator and end user. Featuring ballistically protected walls, glass, and doors, these guardhouses are designed to complement the architecture of the facilities they serve. Factory-assembled Par-Kut security booths have exterior trim below the window line, as well as a decorative parapet around the top that conceals the rooftop air conditioning unit from pedestrian sightlines. Like all Par-Kut buildings, the bullet-resistant booths also include factory-installed electrical systems and are pre-finished in the customer’s choice of color. Visit www.parkut.com to learn more.
 Turnstiles
Turnstiles
Designed Security Inc.’s ES9000 is designed for building lobby applications that call for higher security and high speed throughput while maintaining interior aesthetics. This unit—an IP-based optical turnstile with swing gates—offers a visual and psychological barrier, so incoming pedestrians know authorization is required to enter secured areas. The turnstile can monitor high throughput traffic flow of up to 60 people per minute per lane, and optical sensors and gates make sure that each authorized credential only allows for a single person to enter. The unit can also be customized to meet various security and architectural requirements. Visit dsigo.com/products/optical-turnstiles/ES9000 to learn more. Stand 13114.
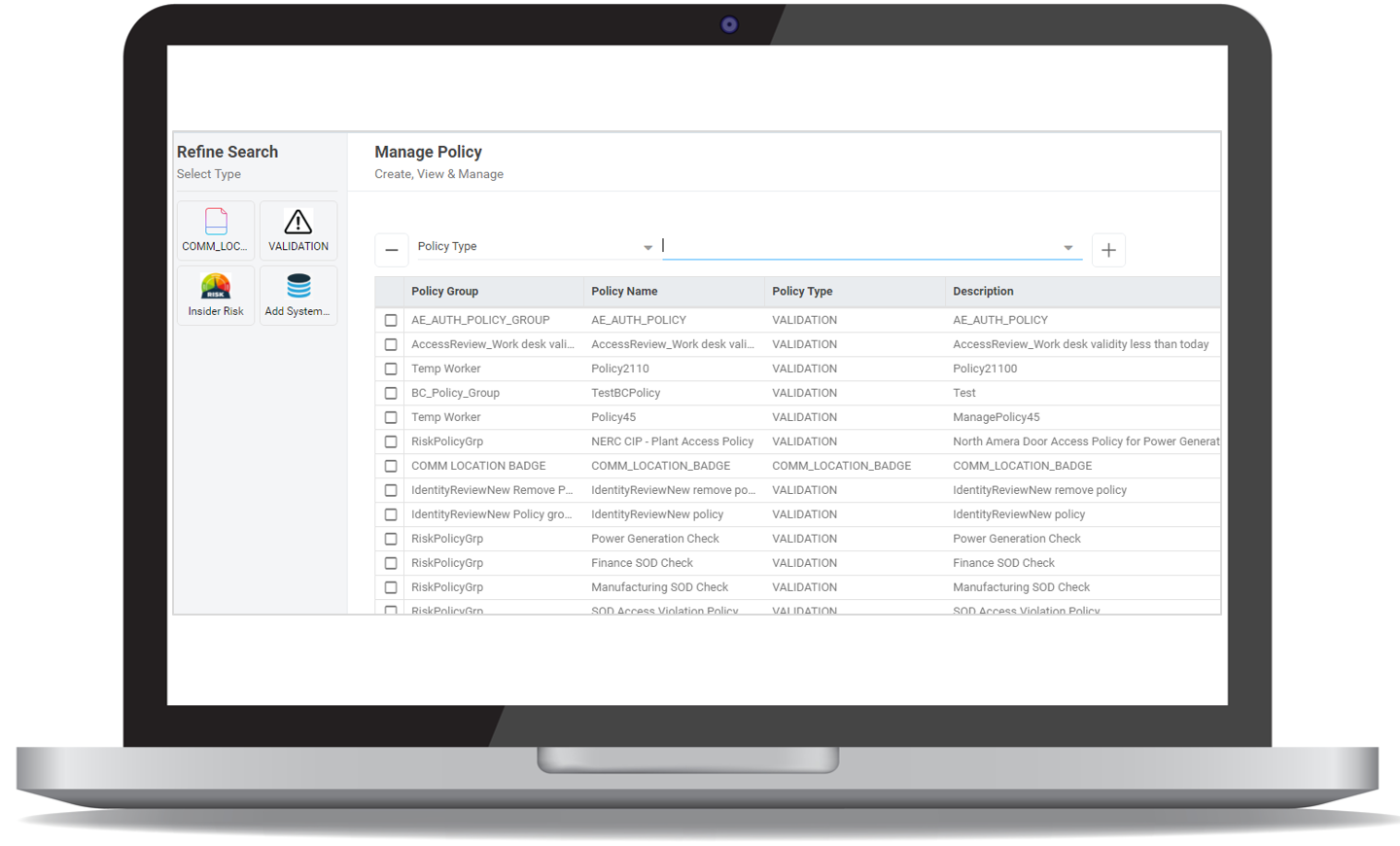 Access Control
Access Control
With policy-based access control (PBAC) from Alert Enterprise, users can adjust to today’s increasing shift to hybrid work environments, adapting to sporadic schedules and overcoming legacy physical access control system limitations and manual requirements. Instead of assigning perpetual access privileges to each cardholder, PBAC offers a cloud dynamic authorization service for physical access. Using identity, roles, and policies, PBAC determines access rights to buildings and physical spaces in real-time without the need to fully replace existing access components. Visit alertenterprise.com to learn more. Stand 6071.
Perimeter Protection
Together with Axis cameras, the Perimeter Defender is an artificial intelligence-based solution that offers analytics gathering intel from the edges of a facility. This solution provides automatic detection and classifies and responds to people and vehicles intruding on a property—giving users the chance to quickly and appropriately respond. The AI-based functionality allows for an easy setup without the need for manual calibration. When used in conjunction with Axis pan-tilt-zoom cameras, thermal cameras, and audio speakers, it offers a system applicable for high-security locations. Visit axis.com/products/axis-perimeter-defender to learn more. Stand 14051.
 Security Operations Center Governance
Security Operations Center Governance
Vector Flow, Inc’s security operations center (SOC) governance application offers security managers a chance to measure, control, and direct SOC operations on a global scale and make proactive decisions. With the SOC governance application, security managers can continuously monitor and assess an organization’s current state, including SLA measurement of alarms, identifying and detecting false and nuisance alarms, and analyzing the performance and outcomes for each SOC technician and SOC itself. Visit www.vectorflow.com to learn more.
 Intelligence Analysis
Intelligence Analysis
Resolver’s risk intelligence platform offers security leaders additional visibility and insights for the chance to allocate resources and make the greatest impact. With applications for incident management, case investigations, security operations, and risk, Resolver offers a wide range of solutions and currently works with more than 1,000 leading organizations. Visit resolver.com to learn more.





