Despite Increased Awareness, Cyber and Business Leaders Struggle to Communicate
In simple terms, what we have is a failure to communicate. Business leaders are increasingly more aware of the cyber risks their organizations face, but cyber leaders continue to struggle to communicate those risks in terms their business counterparts can fully understand and act upon.
The findings come from the World Economic Forum’s Global Cybersecurity Outlook 2023 insight report, a survey of 117 cyber and chief strategy officers from 32 countries, which was published this week during the forum’s annual meeting in Davos, Switzerland.
Respondents confirmed that their cyber and business leaders and boards were meeting to discuss cybersecurity more often but continued to speak past one another in these conversations.
“News about cyber incidents have often dominated the conversation, rather than discussions about why those incidents mattered to an executive’s organization and how precisely businesses could help their cyber leaders manage their responses,” according to the report. “In many organizations, questions about the most recent cyber news continue to drown out conversations on the most important initiatives and investments needed to meaningfully reduce cyber risk.”
This lack of connection and understanding may mean that measures are not implemented to address these threats. For instance, a recent U.S. Government Accountability Office (GAO) report highlighted that it has made 335 public recommendations since 2010 to increase security of federal IT systems and critical infrastructure. Nearly 60 percent of those recommendations, however, have yet to be enacted, partly because they are missing from the White House’s National Cyber Strategy and Implementation Plan.
A Connection Point
There is one area where business and cyber leaders appear to be communicating well: the potential cyber risks related to geopolitical instability. Cyber leaders (93 percent) and business leaders (86 percent) think it is “moderately likely” or “very likely” that geopolitical instability will cause a catastrophic cyber event before 2025.
“Business leaders are often adept at adapting their organizations to new political realities,” the report explained. “This makes geopolitical risk an entry point for the wider conversation between security leaders and business leaders on how cyberthreats are changing and how cyber risk can affect their organization’s business continuity planning.”
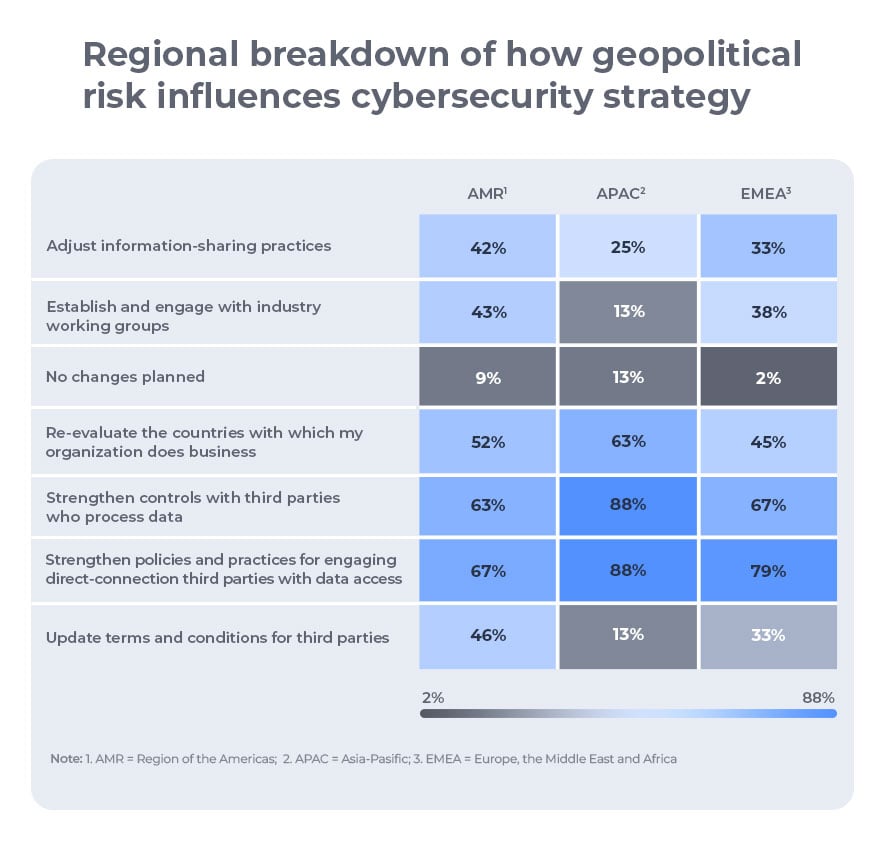
These conversations have resulted in business practice changes, such as strengthening policies and practices for engaging in direct-connection third parties, strengthening controls for third parties who process corporate data, and re-evaluating the countries that the organization does business with.
“Geopolitics arising from the Russia-Ukraine war have also altered how we think about our threat environment,” said one respondent in an interview with the report’s authors. “We have needed to spend time and resources on understanding how the threat landscape has changed, whether the difference in the attacker’s motivation makes us more likely to be targeted, what will be attacked, and how it might be attacked.
“We are now using more resources for active monitoring of the threat picture compared to 12 months ago,” the respondent continued. “We focus on our tactical and short-term (three month) planning and becoming less detailed in our three- to 12-month planning as the environment is so volatile.”
Despite failures to clearly articulate cybersecurity risks so they can be effectively addressed, corporate boards are placing a higher priority on cyber resilience: 95 percent of business executives said cyber resilience is integrated into their enterprise risk-management strategy. They are also creating more opportunities for cybersecurity leaders to brief boards (56 percent meet monthly or more frequently), and chief information security officers are more regularly reporting directly to the CEO.
“More frequent communication means more opportunities to align on cybersecurity priorities,” the report explained. “Perhaps as a corollary, organizational leaders who meet more often are more confident in their organization’s cyber resilience than those who meet less frequently.”
Addressing Pain Points
When looking at why communication failures regularly occur when discussing cybersecurity with executives, the report authors highlighted the difficulty in translating cyberthreats to operational risks and the pattern of expressing costs in “average terms.”
The report authors recommended cyber leaders have access to senior business leadership and use “less technical jargon” when communicating with business leaders. On the flip side, business leaders should be clear about the assets and processes that need to be prioritized for protection from cyber risks.
“Boards should then make themselves accountable for these priorities once they are set because cybersecurity resources are rarely sufficient to effectively defend all parts of an organization all of the time,” according to the report.
An example of this in action is one respondent’s organization created an executive committee to review cybersecurity control exceptions to have greater understanding of how exceptions impact the company’s overall risk posture.
“Now if you need an exception, you will have to come in front of the CTO, CIO, and CISO to defend your case…[The] business might not immediately be ready for the mitigation controls and the path forward, but now I am looking for a mindset shift,” the respondent explained. “When you need to stand in front of three executives, your preparations have to be completely different. We need this to drive cultural shifts towards security.”
Finally, the report recommended organizations and partnerships do more to increase the number of people in the cybersecurity workforce—especially those from underrepresented groups and diverse backgrounds.
“Diversity is not a ‘nice-to-have’ addition to a cyber-skills program but something that is likely to influence the program’s success and also strengthen the cyber resilience of an organization to the highest degree,” the report said. “Employing a range of people with diverse opinions, backgrounds, experiences, and identities leads to stronger outcomes and produces greater insights in any setting, including cybersecurity.”