
Breaching the Gender Gap
Women remain underrepresented in cybersecurity, despite a worker shortage that's leaving thousands of jobs unfilled.
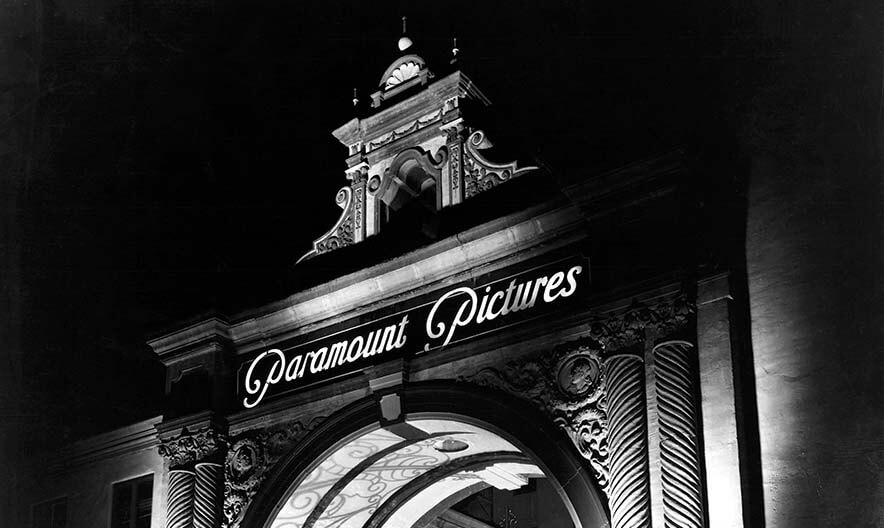
All Secure on Set
Security concerns and protocols are continuously changing in an entertainment climate that considers any and every location for shooting and production.
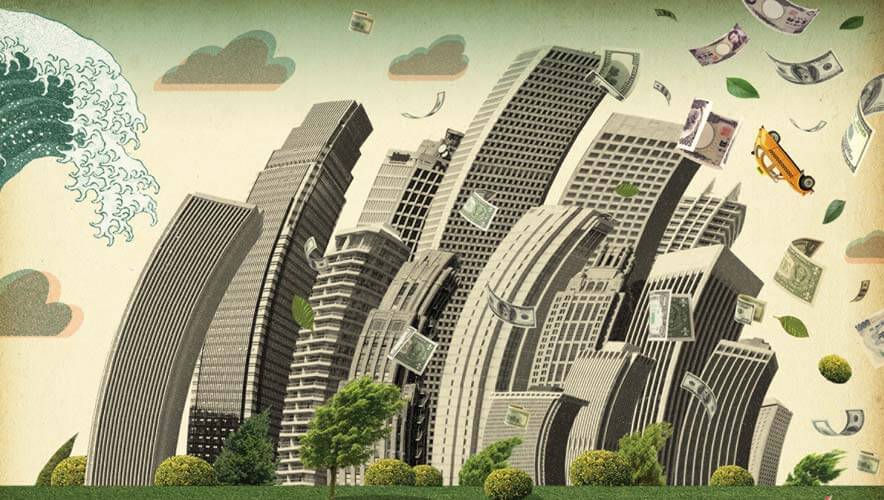
The Calculus of Catastrophe
New research quantifies the economic devastation of natural and man-made disasters and suggests the importance of reducing risk through improved resilience.

Global Nuclear Security
A discussion of the important points of two international summit meetings held in the US in early 2016.
Who's Staying Over?
DHS released a long-awaited report about the number of foreign travelers who overstayed their visas and remain in the United States.

A Casino Makes a Sure Bet
A New Mexico casino upgrades its control room to enhance critical surveillance capabilities.

The OPM Aftermath
A year after the U.S. Office of Personnel Management revealed a massive data breach, critics say more can be done to prevent future attacks.
Editor's Note: Know It All?
Security professionals should be especially wary of the Dunning-Kruger effect when applying their security program to facilities in a different country.
Regional Guidance
Guidance on workforce issues and business climate factors for security managers who may find themselves working in Africa, China, or South America.
Six Food Defense Changes
Six ways the Food Safety Modernization Act rule will require food companies to write a food defense plan to address vulnerabilities in food operations.
Book Review: Beyond Cybersecurity
An excellent overview of IT issues that offers a progressive approach to tackling the evolving landscape of cybersecurity.
Book Review: Keeping Religious Institutions Secure
A resource for those providing security to religious institutions.
Legal Report June 2016
Learn about the latest legislation, regulations, court cases, and judicial decisions affecting security professionals and managers in the June 2016 Legal Report.
ASIS News June 2016
Learn about the latest honors, partnerships, and publications from ASIS in the June 2016 issue of Security Management.
Industry News June 2016
Learn about the latest projects, installations, mergers, acquisitions, and announcements from the security industry.
SM Online June 2016
Dig deeper into the research and reports referenced in the June 2016 issue of Security Management.