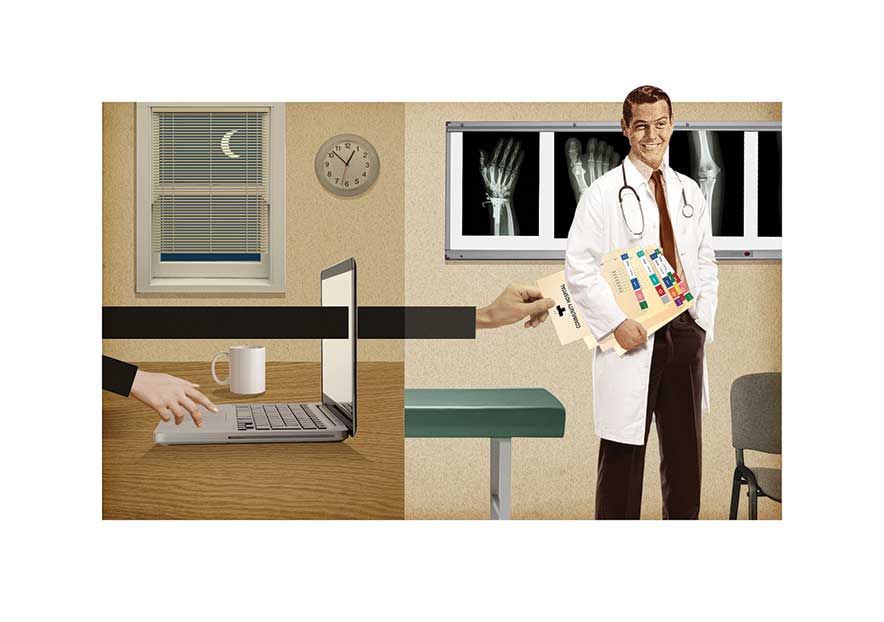
Swiping Medical Data
As if garden-variety identity theft weren’t enough, now criminals are going after your medical records.
It’s happening more and more. A healthcare consumer receives an Explanation of Benefits statement and notices an erroneous charge. At first, the consumer has no idea how to report this, nor to whom. But through trial and error, the consumer pursues the discrepancy and discovers that at some point in the past they have been the victim of medical identity theft.
Alarmed, the victim tries to resolve the issue. The resolution process is long and complex, and it may include embarrassing disclosures of sensitive personal health information. More often than not, the crime is never resolved to the victim’s satisfaction.
Incidents such as the one described above have doubled in the last five years, according to a new study. In 2014 alone, more than 2 million victims were affected by medical identity theft, a 22 percent increase—nearly half a million more victims—compared to the previous year, according to The Fifth Annual Study on Medical Identity Theft, commissioned by the Medical Identity Fraud Alliance (MIFA), a public-private partnership aimed at reducing medical identity fraud. The study was supported by Kaiser Permanente, ID Experts, Experian Data Breach Resolution, and Identity Finder, LLC, and was conducted by the Ponemon Institute.
For the healthcare consumer, this type of identity theft can be an expensive problem. According to the study, 65 percent of the medical identity theft victims surveyed paid more than $13,000 in out-of-pocket costs to resolve the crime. Overall, victims were left facing more than $20 billion in out-of-pocket costs that year.
Moving forward, the increase in medical identity theft incidents is showing “no signs of slowing,” says Larry Ponemon, chairman and founder of the Ponemon Institute.
Why the continued increase in incidents? “One of the main reasons,” says identity theft expert Anthony Perez, “is that the medical industry has lagged far behind most businesses in securing digital records.” The medical industry is fragmented, Perez explains, with many smaller centers and one-doctor practices. Also, many practitioners have failed to educate themselves on how to secure their databases in accordance with the electronic security rules under the Health Insurance Portability and Accountability Act (HIPAA).
Moreover, there are various ways that criminals can access sensitive health information, he adds. Besides computer hacking, one method is going through trash and dumpsters outside of medical buildings, where patient information can often be found.
Sometimes a criminal will walk around a medical facility and take quick serendipitous cell phone photos of unattended computer screens that have information on them. (This technique has also been used in department store hackings, according to Perez.) Occasionally, the photo will even reveal a password written on a sticky note pasted at the bottom of the screen.
Compared with other forms of identity theft, medical identity theft can turn out to be a complicated crime with especially devastating ramifications, experts say. Victims are seldom informed by their healthcare provider or insurer, according to the MIFA study; many victims learn about a crime more than three months after it happens. In the study, about 30 percent of the respondents reported that they never found out exactly when the crime was committed. About 54 percent of the victims realized that a crime had been committed when they found an error in their Explanation of Benefits.
Unlike credit card fraud, where banks are held responsible for false charges, victims of medical identity theft are more likely to suffer significant financial consequences. The number of victims experiencing out-of-pocket costs jumped from 36 percent in 2013 to 65 percent in 2014, according to the study. “The criminal can focus an attack on a single vulnerable individual who has the most to lose, and the fewest resources to address the problem,” Perez says.
Medical identity theft can also damage a consumer’s self-image. Roughly 45 percent of victims reported that medical identity theft affected their reputation in some way, according to the study. Of those, nearly 90 percent suffered embarrassment stemming from disclosure of sensitive personal health conditions, and more than 20 percent said they believed that the theft caused them to miss out on career opportunities or lose employment.
Resolving these problems can be immensely time consuming, and most cases go unresolved, the study found. Only 10 percent of survey respondents reported achieving a completely satisfactory conclusion of the incident. Consequently, many respondents are at risk for further theft or errors in healthcare records that could jeopardize medical treatments and diagnoses.
Two large factors are working against efforts to alleviate the problem, Perez says. One is that the concept of privacy is “under assault.” Companies moving toward use of Big Data want more and more private information for marketing purposes, he explains. And those in the younger generation are collectively so comfortable with social media that many undervalue the concept of privacy. In addition, leaders of new media technology companies sometimes advocate the philosophy of, “if you are not doing anything wrong, you have nothing to worry about,” which is a philosophy that is destructive to privacy, he adds.
Second, the divided and polarized political leadership in Washington has been ineffective in coming up with legislative fixes. “There’s no uniform and consistent message. Everybody has their own silo and they do things differently. They don’t work together,” Perez says.
But whatever happens on the federal level, medical identity theft will be in the public eye moving forward, says Ann Patterson, senior vice president and program director at MIFA.
“The year 2015 will be a year of increased attention to the pervasiveness and damaging effects of medical identity theft,” says Patterson. “As we’ve already seen this year. The healthcare industry is and will continue to be a major target for hackers.”