Enhance your knowledge and decision-making with the latest security research from the ASIS Foundation. Executive summaries are open to all and full reports are complimentary for ASIS members.
The Influence of Security Risk Management: Understanding Security’s Corporate Sphere of Risk Influence
Understand the factors that limit the security function’s influence in corporate risk management and learn strategies to increase the security function’s importance in risk management discussions and decisions.
Read the Executive Summary | Full Report
Findings Modules
Introduction
Finding 1: The Specialist vs. The Generalist
Finding 2: Organizational Leaders See Security as an Operational Risk Concern
Finding 3: Enterprise Security Risk Management (ESRM) Is Not Yet Achieved
Finding 4: Security Professionals Need to Engage Better with Corporate Decision Makers
Finding 5: Security Risk Diagnosis and Security Risk Treatment Are Not a Singular Activity
Finding 6: Organizational Context Has a Significant Impact on Security’s Risk Influence
Finding 7: Security as a Brand Lacks Professional Respect
Finding 8: Language Is a Significant Issue
Finding 9: Influence Is Impacted by Characteristics of the Individual
Empowering Diversity, Equity, and Inclusion in Corporate Security
This Foundation research explores the business case for diversity. It examines the current state of diversity, equity and inclusion (DE&I) in corporate security and discusses best practices that are working to move the needle. The report explores the nature and extent of diversity, the experience of diverse professionals within the industry, the views of security leaders plus the types of initiatives they are spearheading. In addition, it identifies outstanding challenges and makes recommendations for addressing them.
Read the Executive Summary | Full Report
Listen to our new SM podcast Understanding the Diversity Dividend.

The State of Security Management
This study examined the current state of the security profession and delineated eight key findings most crucial to the continued success in security, as well as four noteworthy themes that emerged.
Read the Executive Summary | Full Report
This series of nine short modules (1-4 pages each) highlights the key findings in this report.
Module 1: Overview and Recommendations
Module 2: People Matter
Module 3: Embrace Change
Module 4: Definition of Security
Module 5: Parochialism is a Challenge
Module 6: ESRM
Module 7: Global Perspective
Module 8: Brand and Reputation of Security
Module 9: Security Management Metrics
Security Convergence and Business Continuity: Reflecting on the Pandemic Experience
This research investigates the value and methods of merging business continuity and security, including both physical and cybersecurity. It builds on 2019 Foundation research on security convergence to find out what has changed since the pandemic.
Read the Executive Summary | Full Report
The State of Security Convergence Report
Sponsored by 
Using survey responses from more than 1,000 security leaders in the U.S., Europe, and India, plus more than 20 follow-up interviews, the study provides a ‘current state’ of the relationship among physical security, cybersecurity, and business continuity. It provides relevant benchmarks to compare strategies, plans, and operations and determine best practices for creating more effective and cost-efficient security and risk operations.
Download the complimentary executive summary or receive the full report now available free to ASIS members.
Download (members) | Purchase (nonmembers)
Digital Transformation Series
Using Social Media to Gather Security Intelligence
Artificial Intelligence in Security: Opportunities and Implications
Blockchain: A Guide for Security Professionals
Resilience and Recovery After COVID-19

Resilience, Business Continuity, and COVID-19
To help security professionals benchmark and learn from one another, the ASIS Foundation completed a year-long project that tracked the response, continuity, and resilience of organizations during the worldwide COVID-19 pandemic. Read Article
Campus Security and Student Health at a Technical University
This technical university in southeast Asia—which has a 75-acre campus and serves about 15,000 students—initially treated the COVID-19 outbreak as an influenza event, activating its business continuity practices and assembling its executive level crisis management team.
Preparing to Reopen at a Furniture Retailer
Many retailers of nonessential goods have been forced to close up shop and concentrate on online sales, and this global retailer is no exception.

Intelligent Building Management Systems: Guidance for Protecting Organizations
Produced in partnership with BOMA International (BOMA) and the Security Industry Association (SIA), Intelligent Building Management Systems: Guidance for Protecting Organizations provides a framework for decision-makers to assign a risk-based criticality or impact to their building and asks relevant security questions to develop appropriate mitigation strategies.
The guidance is based on original research that provides an exhaustive overview of identified intelligent building critical vulnerabilities and mitigation strategies.
Download the guidance document, full report, and shareable infographics today!
Scouting the Future
This innovative research initiative identifies seven key change drivers impacting the security profession. Understanding the implications of these changes will allow leaders to better navigate the evolving environment and develop effective strategies for a new, emerging future.
The insights generated will inform the Foundation's research agenda and the ASIS content strategy to meet future member needs. Each change driver represents an area where change is occurring most rapidly and could have the largest impact. To learn more about each topic, please click on the links below.
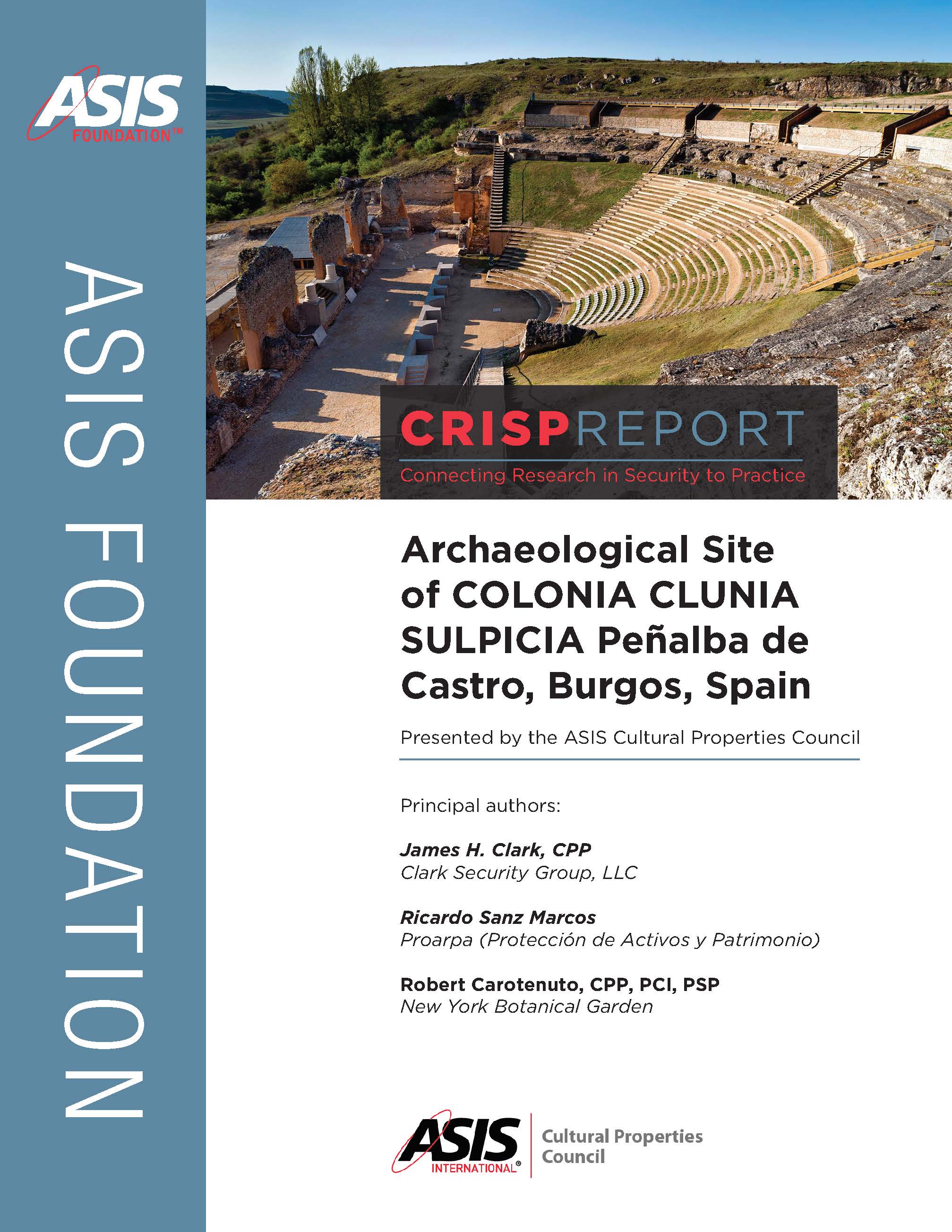
Archaeological Site of COLONIA CLUNIA SULPICA Penalba de Castro, Burgos, Spain
 Principal Authors:
Principal Authors:
James H. Clark, CPP, Clark Security Group, LLC
Ricardo Sanz Marcos, Proarpa (Proteccion de Activos y Patrimonio)
Robert Carotenuto, CPP, PCI, PSP, New York Botanical Garden
Scholars believe that the site of Colonia Clunia Suplicia (Clunia) is the most representative of all the archaeological ruins that have been found from the Roman period in the Northern Iberian Peninsula. The objective of this assessment was to identify those conditions that could create security vulnerabilities for the site and its resources, including people, assets, and activities.
This report provides a case study, including a physical security assessment of Clunia and its surrounding environs, along with a review of other historic sites in the region.
Funded by a grant from the ASIS Foundation and presented by the ASIS Cultural Properties Council.
Persuading Senior Management with Effective, Evaluated, Security Metrics
 The research report Persuading Senior Management with Effective, Evaluated, Security Metrics was sponsored by the ASIS Foundation, in collaboration with the ASIS Defense and Intelligence Council, to add to the body of knowledge about security metrics and to empower security professionals to better assess and present metrics.
The research report Persuading Senior Management with Effective, Evaluated, Security Metrics was sponsored by the ASIS Foundation, in collaboration with the ASIS Defense and Intelligence Council, to add to the body of knowledge about security metrics and to empower security professionals to better assess and present metrics.
This report provides the project's findings, including its three practical, actionable products:
- The Security Metrics Evaluation Tool (Security MET), which security professionals can self-administer to develop, evaluate, and improve security metrics
- A library of metric descriptions, each evaluated according to the Security MET criteria
- Guidelines for effective use of security metrics to inform and persuade senior management, with an emphasis on organizational risk and return on investment
ASIS Foundation Research Process
The ASIS Foundation funds practical, actionable research to benefit the security management profession. The research process is guided by the volunteer Foundation Research Committee. With input from ASIS staff and members, the Committee identifies research priorities for the next 1-2 years. It then develops RFPs (requests for proposals) on desired security management topics and circulates those to the research community. The RFP specifies the research scope, budget, and deadlines.
Potential researchers are invited to submit research proposals in response to the RFPs. The proposals are reviewed and rated by the Research Committee and a final project is selected for funding. A contract is signed with that research team. The Foundation usually funds 2-3 projects per year, depending on budget, and research projects are generally completed in one year or less.
Contact David Brooks for questions about the RFP process or to be added to the distribution list for the next RFP.
- State of security management
- Security risk management
- Emerging security technologies
- Resilience in security
- Diversity, equity and inclusion in security
Submit a Research Topic
-
Prepare a one to two-page overview of the subject including the research questions, how the research would benefit security practitioners, the methodology for the proposed research, and why you believe it is important and timely to address this topic.
-
Send your suggestion to David Brooks, who will share them with the Research Committee for consideration.
-
The Committee will then review the suggestion and may add it to the research agenda for a future project.